Getting Started with the LetsTrust-TPM2Go
Hello Everybody,
here is the short and simple starting guide for the new LetsTrust-TPM2Go USB Stick, (LTT2Go).
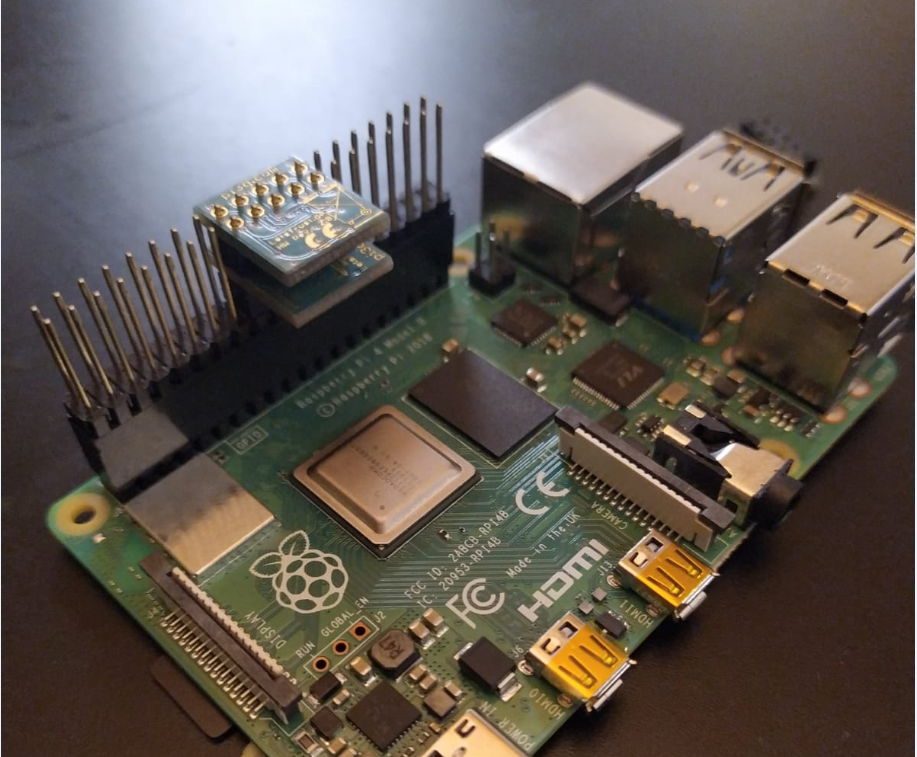
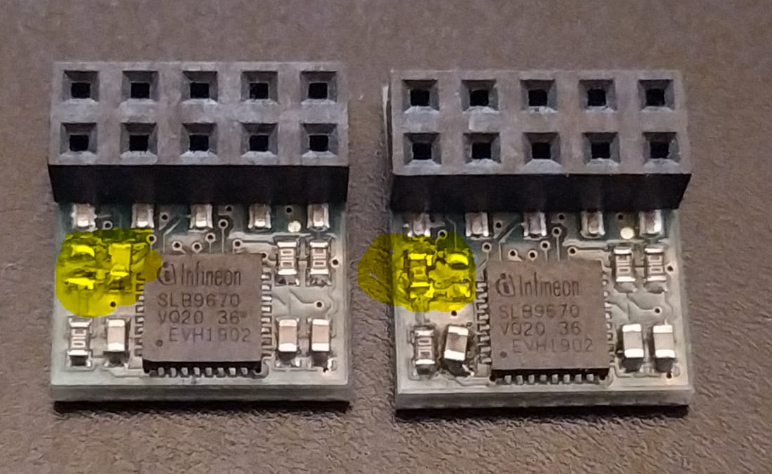
1. As before: You need the Hardware itself, actually buyable here:
https://buyzero.de/products/letstrust-tpm2go
(The list will be updated with every new distributor that we can find)
2. Installation of the TSS and the TCTI-device driver
The simple way to archive a running stack with functional LTT2Go is to install the TSS. Like the LetsTrust-TPM for Raspberry Pi, you could easily use the tpm2_install.sh from https://github.com/PaulKissinger/LetsTrust
This script installs all necessary dependencies for the TSS and the tcti-driver for the LTT2Go, also the abrmd and the tpm2-tools will be installed.
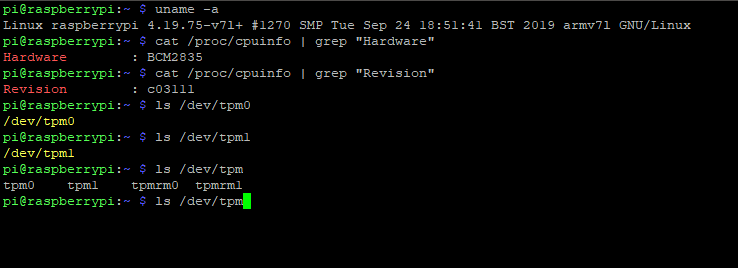
3. Test the function of the LTT2Go:
Follow this https://github.com/tpm2-software/tpm2-tss/blob/master/doc/tcti-spi-ltt2go.md short guide and your LTT2Go should working!
4. Reset the LetsTrust-TPM2Go
https://github.com/PaulKissinger/LetsTrust-TPM2Go Here you'll find a short CLI tool to reset the TPM Chip on the LTT2Go. Use this tool for reboots of the host system or during the development phase. Normally there is no reason to reset a TPM while it is booted up.
That was everything for the short starting guide, and probably also for a long version '^__^.
Bye for now!
Paul
here is the short and simple starting guide for the new LetsTrust-TPM2Go USB Stick, (LTT2Go).
1. As before: You need the Hardware itself, actually buyable here:
https://buyzero.de/products/letstrust-tpm2go
(The list will be updated with every new distributor that we can find)
2. Installation of the TSS and the TCTI-device driver
The simple way to archive a running stack with functional LTT2Go is to install the TSS. Like the LetsTrust-TPM for Raspberry Pi, you could easily use the tpm2_install.sh from https://github.com/PaulKissinger/LetsTrust
This script installs all necessary dependencies for the TSS and the tcti-driver for the LTT2Go, also the abrmd and the tpm2-tools will be installed.
3. Test the function of the LTT2Go:
Follow this https://github.com/tpm2-software/tpm2-tss/blob/master/doc/tcti-spi-ltt2go.md short guide and your LTT2Go should working!
4. Reset the LetsTrust-TPM2Go
https://github.com/PaulKissinger/LetsTrust-TPM2Go Here you'll find a short CLI tool to reset the TPM Chip on the LTT2Go. Use this tool for reboots of the host system or during the development phase. Normally there is no reason to reset a TPM while it is booted up.
That was everything for the short starting guide, and probably also for a long version '^__^.
Bye for now!
Paul